In every SSH/SFTP connection there are four keys (or two key-pairs) involved. This article explains a difference between them and what keys an SFTP client user needs to care about.
The SSH employs a public key cryptography. A public-key cryptography, also known as asymmetric cryptography, is a class of cryptographic algorithms which requires two separate keys, one of which is secret (or private) and one of which is public.1 Together they are known as a key-pair. In SSH, the public key cryptography is used in both directions (client to server and server to client), so two key pairs are used. One key pair is known as a host (server) key, the other as a user (client) key.
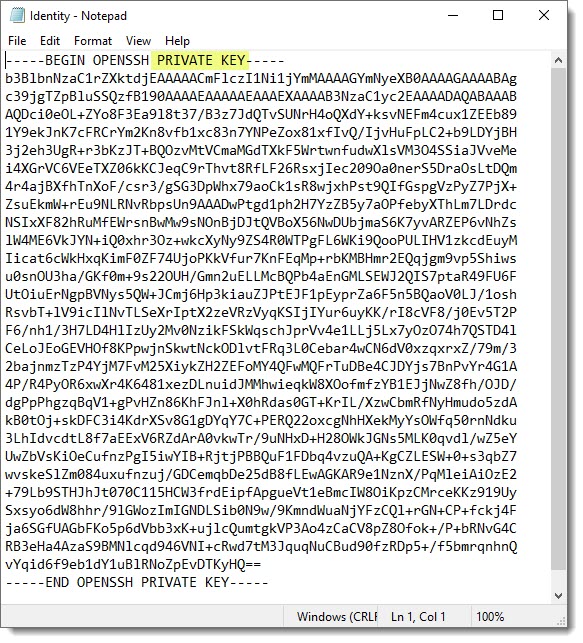
A user private key is key that is kept secret by the SSH user on his/her client machine. The user must never reveal the private key to anyone, including the server (server administrator), not to compromise his/her identity.
- Using PuTTYTray to generate a key pair. If you are running Windows and PuTTYTray for SSH, you can use the built-in key generator from PuTTY to create a new key pair. Click the Keygen button at the bottom of the PuTTY Configuration window to get started. Then in the Key Generator window, check that the Type of key to generate at the bottom is set to SSH-2 RSA.
- Padding for aligning private key to the blocksize; Note that the blocksize is 8 (for unencrypted keys, at least). The RFC 4253 SSH Public Key format, is used for both the embedded public key and embedded private key key, with the caveat that the private key has a header and footer that must be sliced: RSA private keys swap e and n for n and e.
- In this article, we will go through 20 Useful Linux/Unix ssh-keygen command examples. Ssh-keygen command is one of the most used Open source command in Linux Based Systems to generate Public/Private Key pair which can be used for authentication, passwordless login and in many more use cases.

To protect the private key, it should be generated locally on a user’s machine (e.g. using PuTTYgen) and stored encrypted by a passphrase. The passphrase should be long enough (that’s why it’s called passphrase, not password) to withstand a brute-force attack for a reasonably long time, in case an attacker obtains the private key file.
Different file formats are used to store private keys. WinSCP supports PuTTY format, with .ppk extension.
A user public key is a counterpart to user private key. They are generated at the same time. The user public key can be safely revealed to anyone, without compromising user identity.
Generate ssh key without any arguments. You can execute ssh-keygen without any arguments.
To allow authorization of the user on a server, the user public key is registered on the server. In the most widespread SSH server implementation, the OpenSSH, file ~/.ssh/authorized_keys is used for that.
Learn more about public key authentication in general and how to setup authentication with public keys.
Advertisement
A host private key is generated when the SSH server is set up. It is safely stored in a location that should be accessible by a server administrator only. The user connecting to the SSH server does not need to care about host private key in general.
Ssh Private Key Format Example
A host public key is a counterpart to host private key. They are generated at the same time. The host public key can be safely revealed to anyone, without compromising host identity.
To allow authorizing the host to the user, the user should be provided with host public key in advance, before connecting. The client application typically prompts the user with host public key on the first connection to allow the user to verify/authorize the key. The host public key is then saved and verified automatically on further connections. The client application warns the user, if the host key changes.
- The text is partially copied from Wikipedia article on Public-key cryptography. The text is licensed under GNU Free Documentation License.Back
Private keys allow the users to login to SSH without a password. This is considered a safe practice in some cases while also discards the need to remember multiple passwords.
Ssh Using Private Key Example

In this tutorial, we would learn how to generate our own SSH Key Pair on our local machine and then configure our Server to use the same for authentication when trying to connect over SSH.

Steps to Login to SSH Without A Password
Let’s go over the process step-by-step to login to SSH without a password. If you’re new, you can start by reading more about how to connect to a remote host using SSH. If you’re ready, let’s get started.
Step 1: Generate SSH Key Pair
On our local machine, we can generate a SSH Key Pair with the following command :
On execution, we are prompted to specify a file in which to save the private key, the default being /home/user/.ssh/id_rsa ; here id_rsa is the name of our Private Key file. You can always specify a different path and name for the Private Key file. For our demonstration, we shall use the default configuration.
Step 2: Provide A Passphrase (Optional)
Next, we are presented with a prompt that asks us for a passphrase that can be used to protect the SSH Private Key from unauthorized access.
However, this field is optional and if left empty, it stores the Private Key file without any protection. In our example, we would leave this field empty. After this, we would have successfully generated our Key Pair. We are also presented with a ‘fingerprint’ and ‘visual fingerprint’ of our key which we need not save.
Step 3: Configure the Server To Use Our Private Key
At this point, we should have the following two files under /home/user/.ssh :
- id_rsa : Our SSH Private Key
- id_rsa.pub : Our SSH Public Key
Take note of the permissions of the private key ( id_rsa ). SSH Private Key files should ALWAYS HAVE 600 PERMISSIONS! If not, change its permission to the said value using the chmod command:
Next, we need to configure our Server to use our private key for login. Now this can be done manually by logging into the Server and configuring stuff manually but there’s a tool ssh-copy-id which does all the hard work for us !
Hence, to configure our Server to use our private key, simply run :
Here,
- USER is the username we want to login as onto the server
- IP is the IP address of our Server
And with that, we can now simply SSH into our Server with :

If you had previously specified a passphrase, you will get a prompt asking for the same :
Note that if you are not using the default path and file names then you need to specify the private key file using the -i flag as follows :
Thus we successfully SSH’d into our machine using our PRIVATE KEY !
Conclusion
And with that, we were able to login to SSH without a password on our Linux machine. It’s an easy and more secure way of logging in as it locks you to log in from specific IP addresses. If you’re interested in learning more on Linux topics, continue to follow LinuxForDevices.
