AWS Security Fundamentals. In this self-paced course, you will learn fundamental AWS cloud security concepts, including AWS access control, data encryption methods, and how network access to your AWS infrastructure can be secured. We will address your security responsibility in the AWS Cloud and the different security-oriented services available. Hello Dosto.Aj ki video me hum baat karne wale hai ki kya #CloudStorage safe hota hai? Kya cloud par store kiya gaya data safe and secure hai?
So it's more important than ever to keep it secure, private and safe from current and future threats. That's why hundreds of microsoft engineers, scientists and researchers are working to protect you. Inside the high-tech, high-stakes race to. Your cloud infrastructure can be set up to create multiple copies of your data, so if a single machine or even an entire data centre is destroyed for any reason, your data will still be safe. The data centers themselves are physically remote anyway, so it is almost unthinkable that they would be destroyed. Your data is always encrypted with strong 256-bit Advanced Encryption Standard (AES): on your devices, computers and in a cloud. Cloud Synchronization Sync your data automatically with your own cloud account on Google Drive, Dropbox, OneDrive, or even your own NAS server (via WebDAV).
-->Applies to:
Note
The Microsoft Defender Antivirus cloud service is a mechanism for delivering updated protection to your network and endpoints. Although it is called a cloud service, it is not simply protection for files stored in the cloud; rather, it uses distributed resources and machine learning to deliver protection to your endpoints at a rate that is far faster than traditional Security intelligence updates.
Microsoft Defender Antivirus uses multiple detection and prevention technologies to deliver accurate, real-time, and intelligent protection. Get to know the advanced technologies at the core of Microsoft Defender for Endpoint next-generation protection.
You can turn Microsoft Defender Antivirus cloud-delivered protection on or off in several ways:
- Microsoft Intune
- Microsoft Endpoint Configuration Manager
- Group Policy
- PowerShell cmdlets.
You can also turn it on or off in individual clients with the Windows Security app.
See Use Microsoft cloud-delivered protection for an overview of Microsoft Defender Antivirus cloud-delivered protection.
For more information about the specific network-connectivity requirements to ensure your endpoints can connect to the cloud-delivered protection service, see Configure and validate network connections.
Note
In Windows 10, there is no difference between the Basic and Advanced reporting options described in this topic. This is a legacy distinction and choosing either setting will result in the same level of cloud-delivered protection. There is no difference in the type or amount of information that is shared. For more information on what we collect, see the Microsoft Privacy Statement.
Use Intune to turn on cloud-delivered protection
- Go to the Microsoft Endpoint Manager admin center (https://endpoint.microsoft.com) and log in.
- On the Home pane, select Device configuration > Profiles.
- Select the Device restrictions profile type you want to configure. If you need to create a new Device restrictions profile type, see Configure device restriction settings in Microsoft Intune.
- Select Properties > Configuration settings: Edit > Microsoft Defender Antivirus.
- On the Cloud-delivered protection switch, select Enable.
- In the Prompt users before sample submission dropdown, select Send all data automatically.
For more information about Intune device profiles, including how to create and configure their settings, see What are Microsoft Intune device profiles?
Use Microsoft Endpoint Manager to turn on cloud-delivered protection
- Go to the Microsoft Endpoint Manager admin center (https://endpoint.microsoft.com) and log in.
- Choose Endpoint security > Antivirus.
- Select an antivirus profile. (If you don't have one yet, or if you want to create a new profile, see Configure device restriction settings in Microsoft Intune.
- Select Properties. Then, next to Configuration settings, choose Edit.
- Expand Cloud protection, and then in the Cloud-delivered protection level list, select one of the following:
- High: Applies a strong level of detection.
- High plus: Uses the High level and applies additional protection measures (may impact client performance).
- Zero tolerance: Blocks all unknown executables.
- Select Review + save, then choose Save.
For more information about configuring Microsoft Endpoint Configuration Manager, see How to create and deploy antimalware policies: Cloud-protection service.
Use Group Policy to turn on cloud-delivered protection
On your Group Policy management device, open the Group Policy Management Console, right-click the Group Policy Object you want to configure and select Edit.
In the Group Policy Management Editor, go to Computer configuration.
Select Administrative templates.
Expand the tree to Windows components > Microsoft Defender Antivirus > MAPS
Double-click Join Microsoft MAPS. Ensure the option is turned on and set to Basic MAPS or Advanced MAPS. Select OK.
Double-click Send file samples when further analysis is required. Ensure that the first option is set to Enabled and that the other options are set to either:
Send safe samples (1)
Send all samples (3)
Note
The Send safe samples (1) option means that most samples will be sent automatically. Files that are likely to contain personal information will still prompt and require additional confirmation.
Warning
Setting the option to Always Prompt (0) will lower the protection state of the device. Setting it to Never send (2) means that the Block at First Sight feature of Microsoft Defender for Endpoint won't work.
Select OK.
Use PowerShell cmdlets to turn on cloud-delivered protection
The following cmdlets can turn on cloud-delivered protection:
For more information on how to use PowerShell with Microsoft Defender Antivirus, see Use PowerShell cmdlets to configure and run Microsoft Defender Antivirus and Defender cmdlets. Policy CSP - Defender also has more information specifically on -SubmitSamplesConsent.
Note
You can also set -SubmitSamplesConsent to SendSafeSamples (the default setting), NeverSend, or AlwaysPrompt. The SendSafeSamples setting means that most samples will be sent automatically. Files that are likely to contain personal information will still prompt and require additional confirmation.
Warning
Setting -SubmitSamplesConsent to NeverSend or AlwaysPrompt will lower the protection level of the device. In addition, setting it to NeverSend means that the Block at First Sight feature of Microsoft Defender for Endpoint won't work.
Use Windows Management Instruction (WMI) to turn on cloud-delivered protection
Use the Set method of the MSFT_MpPreference class for the following properties:
For more information about allowed parameters, see Windows Defender WMIv2 APIs
Turn on cloud-delivered protection on individual clients with the Windows Security app
Note
If the Configure local setting override for reporting Microsoft MAPS Group Policy setting is set to Disabled, then the Cloud-based protection setting in Windows Settings will be greyed-out and unavailable. Changes made through a Group Policy Object must first be deployed to individual endpoints before the setting will be updated in Windows Settings.
Open the Windows Security app by selecting the shield icon in the task bar, or by searching the start menu for Defender.
Select the Virus & threat protection tile (or the shield icon on the left menu bar) and then the Virus & threat protection settings label:
Confirm that Cloud-based Protection and Automatic sample submission are switched to On.
Note
If automatic sample submission has been configured with Group Policy then the setting will be greyed-out and unavailable.
Related articles
- Help secure Windows PCs with Endpoint Protection for Microsoft Intune]
Raise your security posture with AWS infrastructure and services.
Using AWS, you will gain the control and confidence you need to securely run your business with the most flexible and secure cloud computing environment available today. As an AWS customer, you will benefit from AWS data centers and a network architected to protect your information, identities, applications, and devices. With AWS, you can improve your ability to meet core security and compliance requirements, such as data locality, protection, and confidentiality with our comprehensive services and features.
AWS allows you to automate manual security tasks so you can shift your focus to scaling and innovating your business. Plus, you pay only for the services that you use. All customers benefit from AWS being the only commercial cloud that has had its service offerings and associated supply chain vetted and accepted as secure enough for top-secret workloads.
Benefits
To aid your compliance efforts, AWS regularly achieves third-party validation for thousands of global compliance requirements that we continually monitor to help you meet security and compliance standards for finance, retail, healthcare, government, and beyond. You inherit the latest security controls operated by AWS, strengthening your own compliance and certification programs, while also receiving access to tools you can use to reduce your cost and time to run your own specific security assurance requirements. AWS supports more security standards and compliance certifications than any other offering, including PCI-DSS, HIPAA/HITECH, FedRAMP, GDPR, FIPS 140-2, and NIST 800-171, helping satisfy compliance requirements for virtually every regulatory agency around the globe.
With AWS, you control where your data is stored, who can access it, and what resources your organization is consuming at any given moment. Fine-grain identity and access controls combined with continuous monitoring for near real-time security information ensures that the right resources have the right access at all times, wherever your information is stored. Reduce risk as you scale by using our security automation and activity monitoring services to detect suspicious security events, like configuration changes, across your ecosystem. You can even integrate our services with your existing solutions to support existing workflows, streamline your operations, and simplify compliance reporting.
AWS is vigilant about your privacy. Because our customers care deeply about data security, we have a world-class team of security experts monitoring our systems 24x7 to protect your content. With AWS you can build on the most secure global infrastructure, knowing you always own your data, including the ability to encrypt it, move it, and manage retention. All data flowing across the AWS global network that interconnects our datacenters and regions is automatically encrypted at the physical layer before it leaves our secured facilities. Additional encryption layers exist as well; for example, all VPC cross-region peering traffic, and customer or service-to-service TLS connections. We provide tools that allow you to easily encrypt your data in transit and at rest to help ensure that only authorized users can access it, using keys managed by our AWS Key Management System (KMS) or managing your own encryption keys with CloudHSM using FIPS 140-2 Level 3 validated HSMs. We also give you the control and visibility you need to help demonstrate that you comply with regional and local data privacy laws and regulations. The design of our global infrastructure allows you to retain complete control over the regions in which your data is physically located, helping you meet data residency requirements.
Automating security tasks on AWS enables you to be more secure by reducing human configuration errors and giving your team more time to focus on other work critical to your business. Select from a wide variety of deeply integrated solutions that can be combined to automate tasks in novel ways, making it easier for your security team to work closely with developer and operations teams to create and deploy code faster and more securely. For example, by employing technologies like machine learning, AWS enables you to automatically and continuously discover, classify, and protect sensitive data in AWS with just a few clicks in the AWS console. You can also automate infrastructure and application security checks to continually enforce your security and compliance controls and help ensure confidentiality, integrity, and availability at all times. Automate in a hybrid environment with our information management and security tools to easily integrate AWS as a seamless and secure extension of your on-premises and legacy environments.
Extend the benefits of AWS by using security technology and consulting services from familiar solution providers you already know and trust. We have carefully selected providers with deep expertise and proven success securing every stage of cloud adoption, from initial migration through ongoing day to day management. Choose from our AWS Partner Network (APN), a global program of Technology and Consulting Partners many of whom specialize in delivering security-focused solutions and services for your specific workloads and use cases. APN Partner solutions enable automation and agility and scaling with your workloads. Easily find, buy, deploy, and manage these cloud-ready software solutions, including software as a service (SaaS) products, in a matter of minutes from AWS Marketplace. These solutions work together to help secure your data in ways not possible on-premises, with solutions available for a wide range of workloads and use cases.
Scale Securely with Superior Visibility and Control
With AWS, you control where your data is stored, who can access it, and what resources your organization is consuming at any given moment. Fine-grain identity and access controls combined with continuous monitoring for near real-time security information ensures that the right resources have the right access at all times, wherever your information is stored.
Automate and Reduce Risk with Deeply Integrated Services
Automating security tasks on AWS enables you to be more secure by reducing human configuration errors and giving your team more time to focus on other work critical to your business. Select from a wide variety of deeply integrated solutions that can be combined to automate tasks in novel ways, making it easier for your security team to work closely with developer and operations teams to create and deploy code faster and more securely.
Build with the Highest Standards for Privacy and Data Security
AWS is vigilant about your privacy. With AWS you can build on the most secure global infrastructure, knowing you always own your data, including the ability to encrypt it, move it, and manage retention. All data flowing across the AWS global network that interconnects our datacenters and regions is automatically encrypted at the physical layer before it leaves our secured facilities. Additional encryption layers exist as well; for example, all VPC cross-region peering traffic, and customer or service-to-service TLS connections.
Largest Ecosystem of Security Partners and Solutions
Extend the benefits of AWS by using security technology and consulting services from familiar solution providers you already know and trust. We have carefully selected providers with deep expertise and proven success securing every stage of cloud adoption, from initial migration through ongoing day to day management.
Inherit the Most Comprehensive Security and Compliance Controls
To aid your compliance efforts, AWS regularly achieves third-party validation for thousands of global compliance requirements that we continually monitor to help you meet security and compliance standards for finance, retail, healthcare, government, and beyond.
Strategic Security

AWS is designed to help you build secure, high-performing, resilient, and efficient infrastructure for your applications. World-class security experts who monitor our infrastructure also build and maintain our broad selection of innovative security services, which can help you simplify meeting your own security and regulatory requirements. Our security services and solutions are focused on delivering the following key strategic benefits critical to helping you implement your organization’s optimal security posture:
Prevent
Define user permissions and identities, infrastructure protection and data protection measures for a smooth and planned AWS adoption strategy.
Detect
Gain visibility into your organization’s security posture with logging and monitoring services. Ingest this information into a scalable platform for event management, testing, and auditing.
Respond
Automated incident response and recovery to help shift the primary focus of security teams from response to analyzing root cause.

Remediate
Leverage event driven automation to quickly remediate and secure your AWS environment in near real-time.
Customers
'AWS allowed us to store information in a cost effective manner while alleviating the burden of supporting the necessary infrastructure since AWS takes care of that. It really is a win-win for us and our customers.'
For security and compliance, customers choose AWS.
Partners
APN Partners offer hundreds of industry-leading security solutions that help customers improve their security and compliance. The scalability, visibility, and affordability our partners inherit with the cloud enables them to create world-class offerings for customers. Learn about products and solutions pre-qualified by the AWS Partner Competency Program to support you in multiple areas, including: infrastructure security, policy management, identity management, security monitoring, vulnerability management, data protection, and consulting services.
These products complement existing AWS services to help you deploy a comprehensive security architecture and a more seamless experience across your cloud and on-premises environments. In addition, refer to our Security Solutions in AWS Marketplace for a broad selection of security offerings from hundreds of independent software vendors.
Network and Infrastructure Security
Network inspection designed to detect and protect your workloads from malicious or unauthorized traffic.
Host and Endpoint Security
Agents that detect and protect against malware and other threats found on your operating system or host. Includes AV, EDR, EPP, FIM, and HIDS.
Data Protection and Encryption
Helps protect data via encryption, user behavior analysis, and identification of content.
Governance, Risk and Compliance (Technology Partners)
Helps provide analysis to assess controls or AWS policies (IAM, S3) as well as regulatory frameworks such as PCI, GDPR, and HIPAA.
 Learn more »
Learn more »Logging, Monitoring, Threat Detection, and Analytics
Centralized logging, reporting, and analysis of logs to provide visibility and security insights.
Identity and Access Control
Help define and manage user identity, access policies and entitlements. Helps enforce business governance including, user authentication, authorization, and single sign on.
Vulnerability and Configuration Analysis
Help inspect your application deployments for security risks and vulnerabilities, while providing priorities and advice to assist with remediation.
Application Security
Assesses code, logic, and application inputs to detect software vulnerabilities and threats.
Consulting Partners
Providing expert guidance to AWS customers on how to leverage security tools and embed best practices into every layer of their environment.
Learn more »Security Engineering

Accelerating people and processes with modern security tools and frameworks to provide security capabilities that are uniquely available on the AWS Cloud.
Governance, Risk and Compliance
Demonstrable success in helping customers navigate and achieve successful audits and accreditation to industry assurance and certifications programs.
Security Operations and Automation
Proven capabilities of building scalable solutions for customers across all industry verticals and expertise in building secure infrastructure, environments, and applications from the ground up.
AWS RE:INFORCE
Join our email list to be the first to receive details about re:Inforce 2021
Learning
Learn about cloud security with resources such as whitepapers, videos, articles, blog posts, training, and documentation. Learn more >>
How to Enable Encryption in a Browser with the AWS Encryption SDK for JavaScript and Node.js
In this post, we’ll show you how to use the AWS Encryption SDK (“ESDK”) for JavaScript to handle an in-browser encryption workload for a hypothetical application.
AWS Security Blog >>Introduction to AWS Security
AWS’s approach to security, including the controls in the AWS environment and some of the products and features that AWS makes available to customers to meet your security objectives.
AWS Security Fundamentals
In this self-paced course, you will learn fundamental AWS cloud security concepts, including AWS access control, data encryption methods, and how network access to your AWS infrastructure can be secured. We will address your security responsibility in the AWS Cloud and the different security-oriented services available.
AWS Training Course >>Free Digital Training
Learn with hundreds of free, self-paced digital courses on AWS fundamentals.
Learn more >>Classroom Training
Deepen your technical skills and learn from an accredited AWS instructor.
Learn more >>AWS Certification
Validate your expertise with an industry-recognized credential.
Learn more >>What's new in Security, Identity, & Compliance?
View all >>Expert Guidance
Security support
- Real-time insight through Trusted Advisor
- Proactive Support and advocacy with a Technical Account Manager (TAM)
Professional services
- Strategic advice for In-Depth Security Solutions
- Detect and respond to security issues with the Security Operations Playbook
Vulnerability Reporting
Learn about our practice for addressing potential vulnerabilities in any aspect of our cloud services.
Report vulnerabilities
AWS investigates all reported vulnerabilities
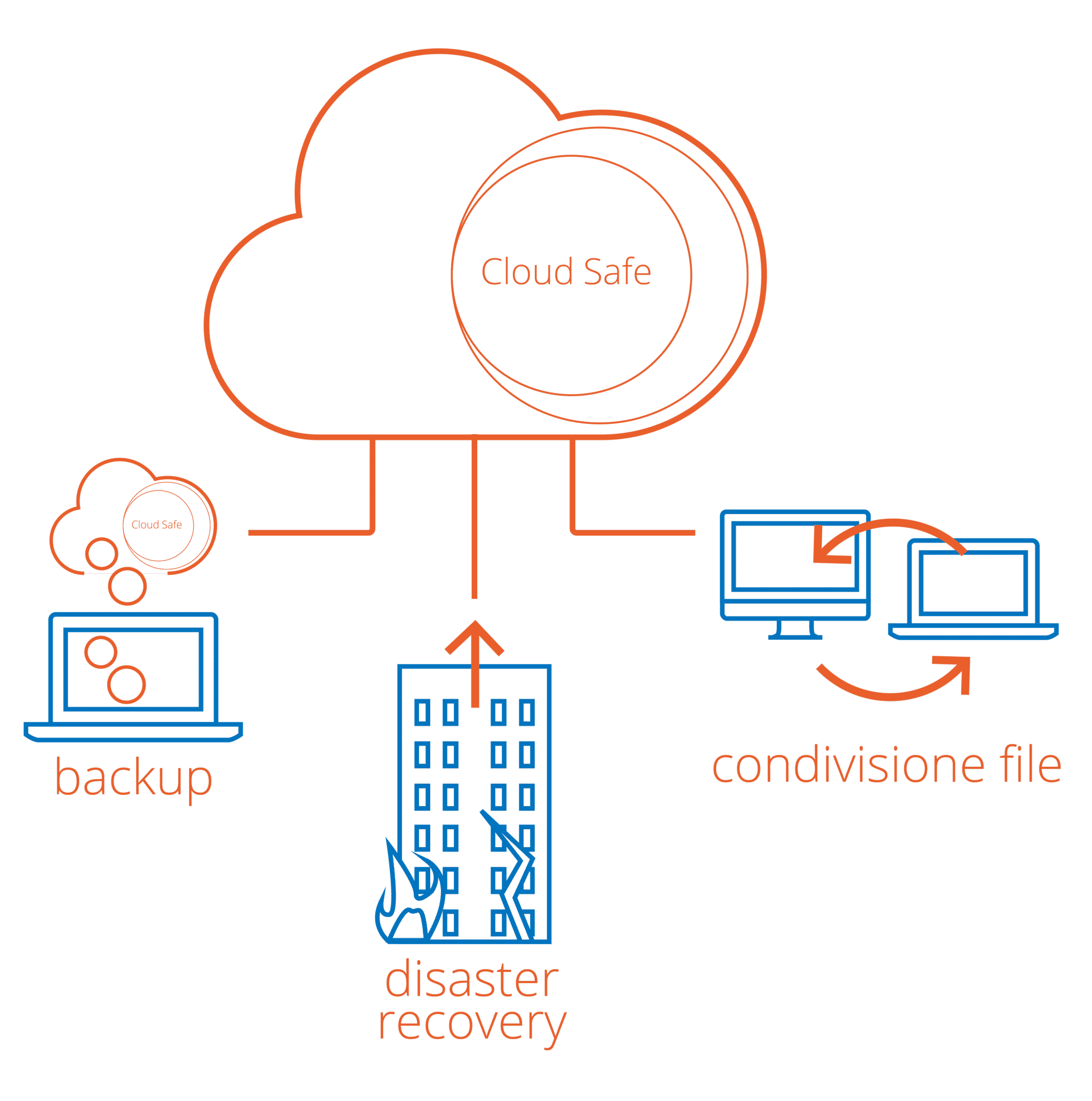
Safe Cloud Storage
Report suspicious emails
Please notify us of any suspicious emails
Are Cloud Storage Safe
Follow us on Twitter »